DEV update: New authentication API call limits
Starting in November 2016, Geotab will introduce API call limits on the number of Authentication requests it will accept, to ensure optimal performance.

Vice President, Software Development at Geotab
Oct 31, 2025

For many companies, APIs are now a central part of doing business. The API economy is thriving — look at Amazon, Salesforce, and Twitter. IBM has written that APIs are transforming business and they are “the digital glue that links services, applications and systems.” Expandability is one of the pillars of Geotab telematics — our secure open platform with free APIs, software development kit (SDK), and Marketplace are evidence of that.
Many customers and partners rely on Geotab’s APIs to unlock more value from their telematics data. Application programming interfaces (APIs) make it possible to automate processes, integrate, and simply manage your data as you like. Ensuring that developers and businesses can connect with their data easily requires constant diligence from our team. Geotab continuously monitors API calls.
Therefore, to safeguard optimal functioning and ensure that poorly written MyGeotab SDK applications do not impact the overall system performance, Geotab will be setting a limit on Authentication calls.
Important Notice on Authentication API Call Limits
Starting in November 2016, the MyGeotab API will enforce limits on the number of Authentication requests it will accept.
This change will start rolling out in November 2016 for new customers, and will be fully enforced for all customers by end of January 2017.
Questions and Answers About the Authentication Call Limit
Q: How will the Authentication calls limit affect MyGeotab users?
A: This change should not affect normal usage of the MyGeotab system. If you are using the MyGeotab SDK to make API calls, this may affect you.
Q: What is the limit? How many calls will be allowed?
A: No more than 10 Authentication requests per minute for a user are allowed. Both successful and unsuccessful Authentication calls count towards the limit.
Q: Does this affect other API calls, like Get<Device> or GetFeed<LogRecord>?
A: No, the limit applies to Authentication calls. Once authenticated, you can consume other API calls as needed. Note: Geotab actively monitors API calls. If any API abuse is suspected you will be notified.
Q:What happens when I go over the Authentication limit?
A: The server will return an OverLimitException.
Q: What should I do if I get an OverLimitException?
A: Review the Authentication section in the SDK documentation first. Your application should be using the credentials object that is returned from an Authentication request for subsequent calls. It contains a token that confirms your identity for subsequent operations. If it expires or a database is moved, a new Authentication call should be made. This approach allows for efficient usage of Authentication requests.
Q: Do I need to contact someone or do something if my limit is exceeded?
A: No, your application logic should be modified (as per above) or you are trying to Authenticate with incorrect credentials. It will automatically reset every minute.
Q: If I’m using Geotab.Checkmate.ObjectModel.dll, do I need to change anything?
A: The .Net assembly provided by Geotab already has built-in logic for handling Authentication, credentials expiry and database moves efficiently. When used correctly, no changes are needed. However, it is still possible to write code that constantly make Authentication calls for every operation.
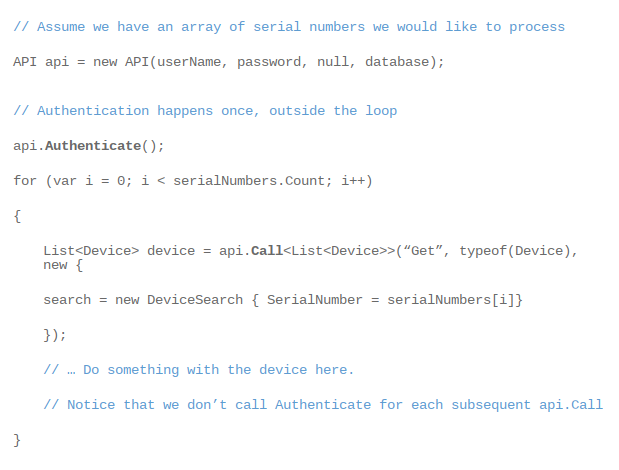
Q: Can you give me an example of how it should be done?
A:
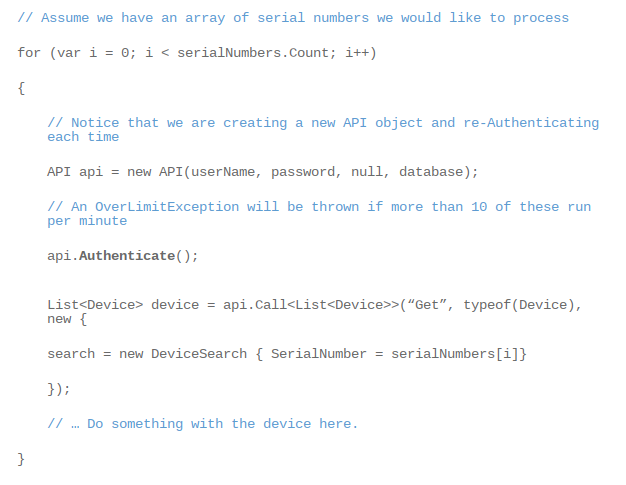
Q: Can you give me an example of how it should not be done?
A:
Watch this DEV Channel video to learn more about making your first API call.
Subscribe to get industry tips and insights

Vice President, Software Development at Geotab
Pieter Venter is Geotab’s Vice President of Software Development and has been building large-scale software solutions for over 20 years.
Table of Contents
Subscribe to get industry tips and insights
Related posts
.jpg)
Trailer telematics: How fleets track and manage trailers in real time
June 2, 2026
4 minute read

What astronauts and Axon Week taught me about public safety
May 21, 2026
4 minute read

Why field service routing decisions are costing you more than fuel (and how to fix it)
May 14, 2026
4 minute read

Cargo theft prevention has entered the AI era. Is your fleet keeping up?
May 11, 2026
4 minute read

How fleet telematics helps protect police officers and build community trust
May 11, 2026
4 minute read
Why maintenance scheduling for fleet assets requires more than a calendar
May 7, 2026
5 minute read