Dialing down risk with audit logs
Are you reviewing your audit logs? Learn the three key benefits of the Audit Log report in MyGeotab fleet management software
By Geotab Team
Aug 21, 2024

Among the many responsibilities of fleet managers is maintaining security of the system and managing risk. One tool that can be useful in this effort is the Audit Log report in MyGeotab fleet management software.
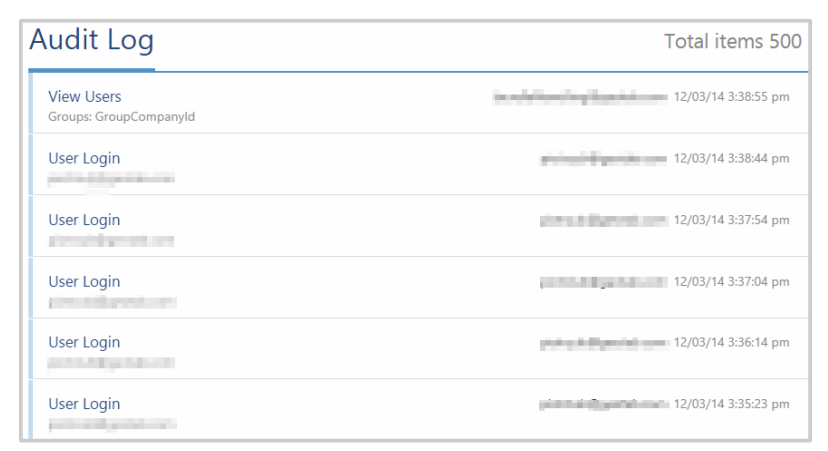
Fleet managers or database administrators can track changes, activities, and all notable events which have occurred in MyGeotab with the Audit Log. Having access to a quick snapshot of user activities is important, especially if multiple users have administration access.
Three key benefits of using the Audit Log report:
- Ability to monitor system usage by staff
- Better risk management
- Increased security
Creating an Audit Log Report in MyGeotab
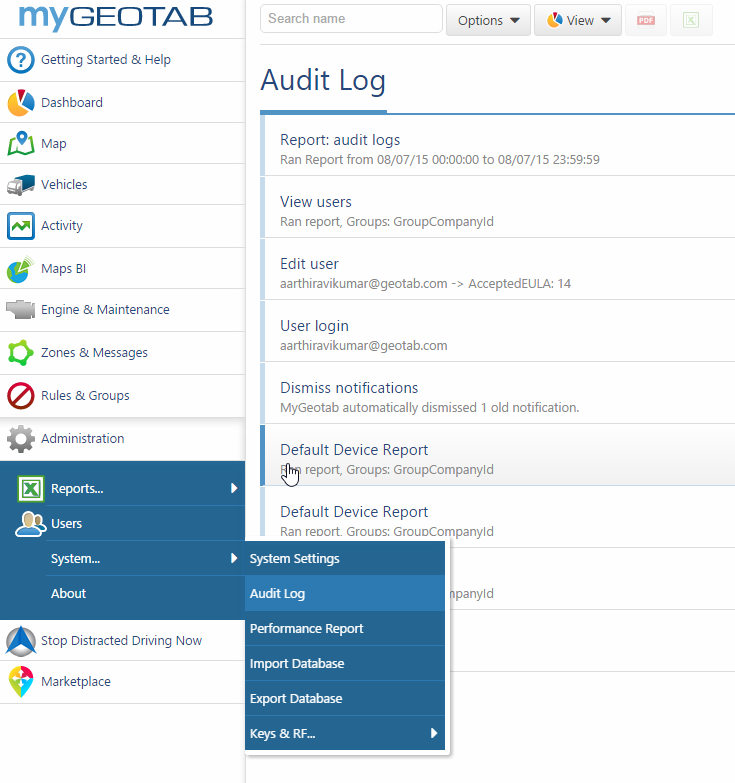
The Audit Log report is a default report in MyGeotab. To view the Audit Log, go to Administration > System > Audit Log.
Note: The Audit Log is just one of the many default reports in MyGeotab. To learn more about default reports, what they are used for and how to customize them, watch the webinar MyGeotab Default Reports.
How Can I See User Activity in MyGeotab?
The Audit Log makes it easy for a fleet manager to see what team members are doing by providing details on what all users of the database have viewed, edited, added, or removed. Armed with this information, a fleet manager can identify errors or misuse and give users further instruction on how to perform tasks correctly. The oversight also increases the sense of individual accountability among users.
When creating the Audit Log report, you can select from many different audit types. Plus, as new features are added to MyGeotab, more audit type options will be also become available.
Some examples of user activities you can track:
- User login and logoff
- View, Remove, Add and Edit user, device, zone, route or exception rule
- Remove, Edit and Add HOS log or DVIR log
- Remove, Add or Edit fuel transaction
- Send, Delete or View message
- Change asset, driver, defects, repaired by or certified by
- Upgrade server, Upgrade, Migrate, Export or Import database
- Password Reset Request
A great embedded analytic tool is the Advanced Audit Log report, which can be found on the Audit Log page, by clicking View > Advanced. This report depicts a bar graph representation of the activity events of each user in the portal.

Identifying Problems and Managing Risk
Audit Log reports are very useful in risk management as they help track how a problem or error has occurred. By checking the logs, administrators can have a better understanding of what the cause for the problem was, what the original settings were, and how to fix it. Going through this exercise makes it possible to set up preventative measures to avoid similar situations in the future.
For example, if a particular rule has been changed by a user, all previously logged exception events will be removed for that rule. The audit log report records the date and time when the rule was modified. With this information, data can be re-processed to reflect the new rule.
Another instance of where an audit log is beneficial is if a device is no longer visible in the Vehicle page. In this case, the Audit Log will show whether the device was made historic, will indicate the date and time this event occurred, identify the user who made the change or perhaps accidentally removed the device. A fleet manager can use this information to follow-up, restore the device, and retrieve lost data.
Stronger Security with Audit Logs
Fleet managers can include Audit Logs as part of their overall plan for security, and maintaining transparency and accountability. All access into a customer database is audited and stored indefinitely within the database Audit Log for the customer to see.
Companies can use the Audit Log to look for potential security breaches by monitoring who has access to what information in the database and keeping a record all users who have logged into the database. All events are documented, such as Add, Edit, View, Report, and Remove activities.
The Audit Log also plays a role in upholding a driver identification system. If a driver attempts to use their driver key before it is assigned to their user account, a log will be created in the Audit Log to indicate that an unassigned key has been used to identify a driver in a vehicle.
Specific MyGeotab security features related to Audit Logs:
- All user activities in MyGeotab are logged and can be viewed by any approved users within the MyGeotab audit log.
- Audit log data cannot be altered or removed.
- MyGeotab offers highly flexible rights management, to allow limited access to various areas within the system, for specific users;
- Customer data is completely isolated from other customer data, i.e. information (GPS data, user info, exception rules, et al.) stored in a customer database is not accessible or available to other databases, even if the two databases are on the same physical server; and
- Only authorized Geotab employees are able to connect and log into all hosted databases for troubleshooting purposes, all of which is fully audited and logged within the audit log.
Audit Logs are part of the numerous security measures taken by Geotab to prevent unauthorized access into the MyGeotab system. Geotab strives to provide accountability for all user activity in order to ensure a safe and reliable platform.
For more detailed information on Geotab’s security, please review the security policy guide and subscribe to our blog for updates on Geotab data center security.
To learn more about database security and monitoring, please post your questions in the comment box below.
Related Posts:
Geotab Datacenter Expands in 2015
Better Fleet Management With Advanced Exception Reporting Technology
Subscribe to get industry tips and insights
The Geotab Team write about company news.
Table of Contents
Subscribe to get industry tips and insights
Related posts

Maintenance log template: How fleets track repairs, stay compliant and cut costs
June 3, 2026
5 minute read

The size myth: Why intelligence, not inventory, is driving 2026 leasing profits
May 13, 2026
4 minute read
Why maintenance scheduling for fleet assets requires more than a calendar
May 7, 2026
5 minute read

What is condition-based maintenance? How it works, tools and how to start
May 1, 2026
8 minute read

How fuel transaction controls help fleets manage costs in a volatile market
April 28, 2026
3 minute read

The 'ghost fleet' crisis: Why idle rental cars are your biggest liability
April 27, 2026
4 minute read